US: Chinese hacker I-SOON internal documents to be analyzed
・I-SOON internal documents were exposed on GitHub
・I-SOON’s customers include the Chinese military, police, and intelligence agencies.
We bring you a summary of articles published in NTDTV Japan.

CNN in the US:
On February 22, it was reported that the Biden administration has begun investigating the leak.
US government official:
Started analyzing leaked documents from Chinese hacker I-SOON.
Unraveling the hacking methods of Beijing, China.
https://www.epochtimes.jp/2024/02/207449.html
Exposed I-SOON internal documents:
On February 27th, I-SOON hacking information (=confidential information from various countries around the world) was exposed on GitHub.
Taiwanese researchers discovered:
On February 16th, researchers from Taiwan. Found on American software GitHub.
Hundreds of pages of I-SOON internal documents and employee chat logs.

National Defense Strategy of Taiwan: Director Su Ziyun
What is I-SOON?
Ostensibly, it’s a security company based in Sichuan, China.
In reality, a hacking service is being developed in Shanghai.
They are an Advanced Persistent Threat (APT) group.
1. I-SOON follows orders from the Chinese Communist Party and steals large amounts of data.
2. Hacker attacks on government agencies, organizations, and individuals around the world.
3. China outsources espionage services to private companies. This is clear public evidence.
I-SOON Sichuan branch contract:
Details of the contract for I-SOON’s Sichuan branch office from 2016 to 2022 have been revealed.
I-SOON contract released:
The history of the I-SOON site has been released as a screenshot.
1. I-SOON’s customers are the Ministry of Public Security of the Communist Party of China and the public security departments of provinces and cities.
2. The main users are the Chinese police, intelligence agencies, and Chinese military.
3. The contract amount is low at $1,400. However, the hack to the Vietnamese government cost $55,000.
Comments from Director Su Ziyun:
It can be said that this internal document is not a forgery.
1. The credibility of the documents is extremely high, from technical aspects to corporate management.
2. You can even see the logical connections between internal employee conversations.

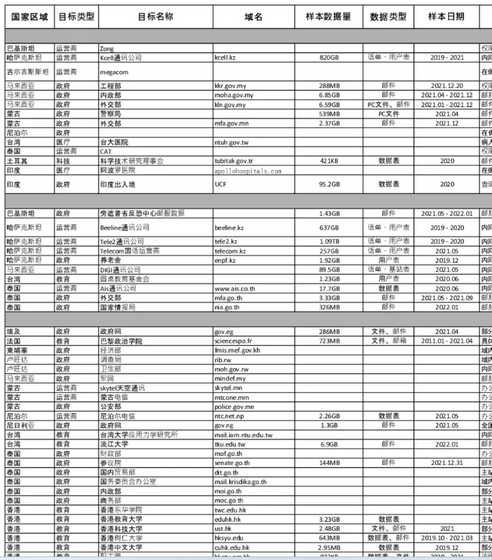
List of exposed documents:
This time, 190MB of internal data from over 570 cases was leaked.
These include document files, images, chat logs, etc.
The Washington Post:
I-Soon provides customers with Taiwan’s transportation network and geographic data (459GB). This data will be useful in China’s invasion of Taiwan.
Leaked conversation record:
There are also conversation records that show that I-Soon was in contact with APT 41.

1. Countries with close ties to the Chinese Communist Party:
I-Soon hacked India, the UK, Hong Kong, Taiwan, and South Korea.
2. Targeting 80 government agencies:
Indonesia, Vietnam, Cambodia, Mongolia, Myanmar
Malaysia (Ministry of Foreign Affairs and Ministry of Defense), Thailand (National Intelligence Agency),
Government agencies in Rwanda and Nigeria, etc.
3. Institutions and organizations in each country:
Indian Reserve Fund, Indian Immigration Data、
Taiwanese hospital and transportation data,
Korean provider call records,
Vietnamese airline passenger ID and destination information
Tibetan group,
Until the University of Hong Kong after the Hong Kong democracy movement,

US Department of Justice: Indicting APT 41:
In 2020, the US Department of Justice indicted five members of the Chinese hacker APT 41.
5 Chinese hackers:
All of them are from an internet company called “Chengdu 404” in Sichuan province.
I-SOON is a client of Chengdu 404:
According to leaked documents, I-SOON has business with Chengdu 404.
Founder of I-SOON: Haibo Wu
The founder of I-SOON was also acquainted with APT 41.
